| *2 | Software such as Java, Flash, Adobe Reader/Flash Player, Internet browsers, etc. |
Security KDDI Cloud Inventory
A unified cloud management service for device security

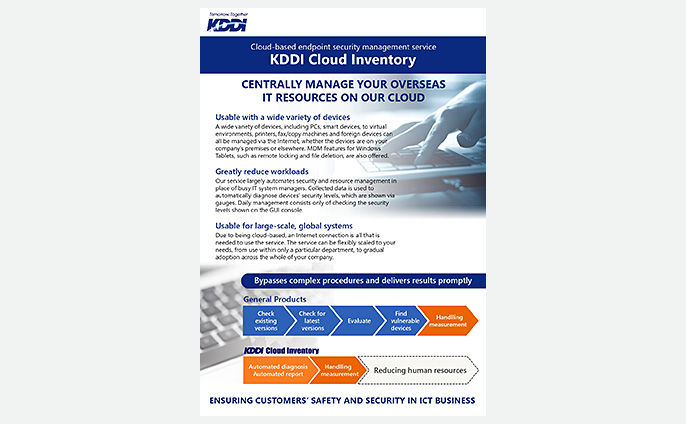
KDDI Cloud Inventory provides centralized endpoint security, such as IT asset management and detection of security policy-violating clients.
An optimal solution for those troubled by these issues

How can I manage the security of PCs taken off company grounds?

How can I check for devices that violate company policy?

How can I stop privately-owned smartphones from connecting to the company network?
Product overview
Unifies your device security process
Usable from anywhere
Manage from anywhere in the world where you have an Internet connection
Multi-device support
Manage multiple device types, including Windows devices, Mac devices, and mobile devices
Automated security management
Automatic detection and display of devices with security vulnerabilities
3 languages supported
A Web console available in Chinese, English and Japanese
Global contracts
Purchase with a single Japan contract, or purchase through local contracts in other countries’ currencies
Wide variety of security controls
External device restrictions, unauthorized device detection and blocking, behavioral detection and other security features

Features
Functionality
A wide variety of security-related functions
In addition to security management, KDDI Cloud Inventory provides HDD encryption, external device (USB memory, etc.) restrictions, PC operational log acquisition, behavioral detection (malware detection), and more.

Efficiency
Make large reductions in your workload
Automation of security management (automatic vulnerability diagnoses) and asset management frees up your busy system administrators and makes usage easy.
Automatic vulnerability diagnoses
Provides a list of PCs lacking the latest OS and software*2 updates. By automatically located at-risk PCs, your management workload is greatly reduced.
Asset management
Once a day, information is collected from your managed devices, allowing you to manage your assets with accurate information, without the work of collecting it yourself.

Flexibility
Cloud-based system means you can start small
All you need is an Internet connection. Easily scale as needed, from managing a few dozen devices to tens of thousands.

Please consult a KDDI consultant.
Brochures
Related Case Study

Related Knowledge Articles
What is the best solution for your problem?
Please consult a KDDI consultant.